What is Pegasus spyware software?
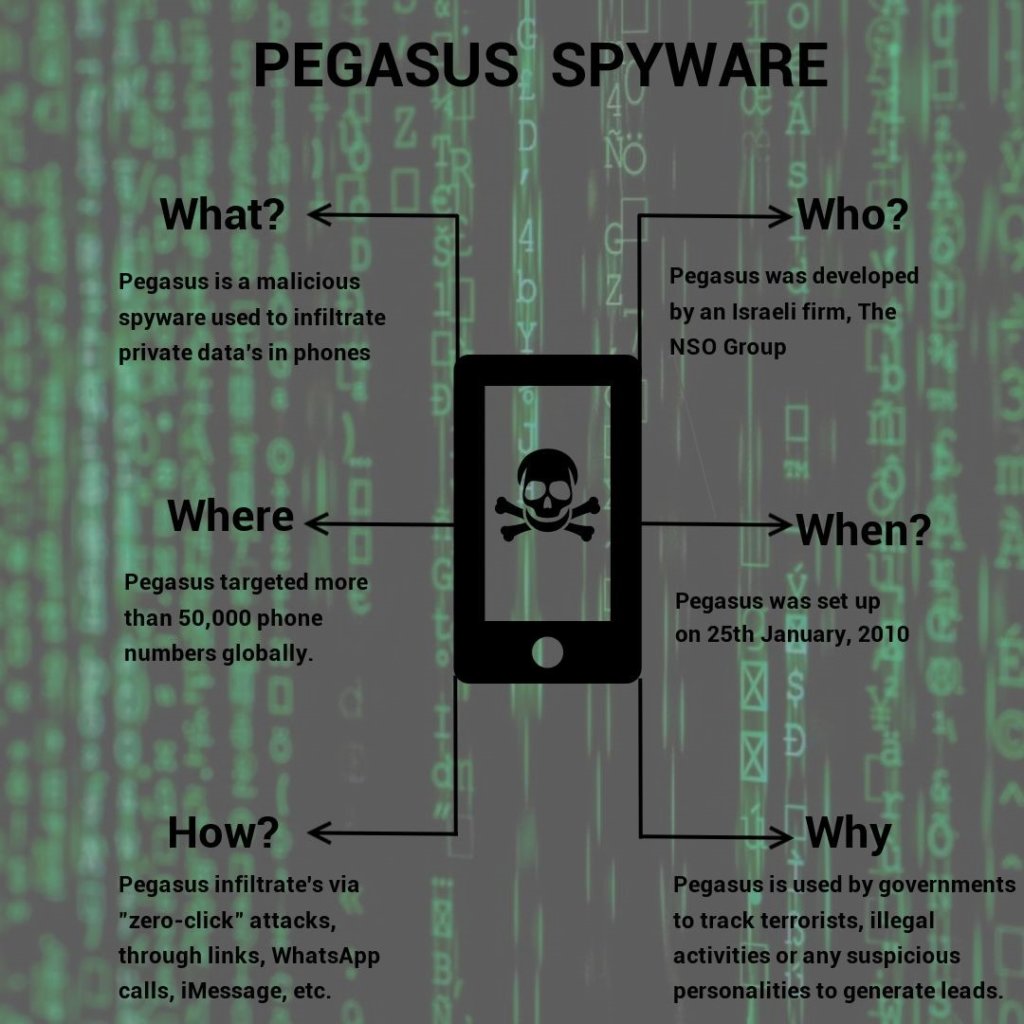
Pegasus, a malicious software created by the Israel’s NSO Group, has been found to be used by governments around the world according to a major journalistic investigation. Pegasus is used as a spying software that infects the phones of targets through various mechanisms after which the victims’ phones can be controlled without them having any knowledge about it. The powerful hacking tool can be employed to set out surveillance, collect information, and track movements of the user after their phone has been infected by the Pegasus software. While it can be used to spy on any terrorist suspects related to national security, but misuse of such technology can also be used to suppress politicians, lawyers, activists, and other such parties.
Who can use Pegasus?
Recent reports have shown this software to be used by several governments for different purposes. It is alleged that Saudi Arabia used this same software to aid the assassination of their biggest critic journalist, Jamal Khashoggi, which was one of the most controversial news in 2018. Pegasus can be a useful weapon for any organization that is trying to suppress and eliminate threats to them. However, it is a powerful tool for governmental spy agencies to maintain national security and intercept leads, suspects, or any useful information which would have been impossible otherwise to breach encryption technology.
Which organization made Pegasus and why?
Pegasus was invented by Israel’s NSO Group which acts as a private contractor for Governments to supply spyware technology for hire. NSO only intents its products to aid government intelligence and law enforcement agencies to use this technology for the purpose of tackling terrorism and illegal activities and has stated that it will cut off an agency’s access to Pegasus if there is evidence of abuse related to the software’s use.
How does it infiltrate devices?
Any user can simply send a malicious link to anyone, which if clicked, will give way to the Pegasus spyware to infiltrate their phone without coming in the notice of the victim. This was the initial method of administrating Pegasus software into someone’s phone. However now, the spyware can get into someone’s phone without even interacting with the victim via a zero-click attack that exploits bugs in popular apps. This could be through WhatsApp calls, iMessage, and even facetime. Pegasus infiltrates by finding vulnerabilities of these apps and using its protocols after which the user doesn’t even have to open a link, read a message, or pick a call.
Why protecting data is so important?
We are living in the “Internet of Things” era where data is one of the most valuable assets of an organization and protecting it is a top priority. User data accounts for communications, databases, infrastructure, transactions, and knowledge, and much more in an organization. Regardless of legal or regulatory constraints, it is in a company’s best interests to keep its data secure. The volume of data crossing the network via cloud and data center environments has increased.
According to the Economist, we are now living in the “zettabyte era.” For traffic being generated, the most suitable step is to control and protect the transfer of sensitive or personal information at every known location. Protecting data from internal or external corruption and unauthorized access protects a business from financial loss, reputational damage, consumer confidence degradation, and brand erosion.
Leverice, a secured cross-communication messaging platform allows users to communicate at their own pace. This is accomplished by allowing users to organize chat content into nested sub-channels on the site. Users are in charge of organizing the flow of information rather than being exposed to incessant noise from every team. Leverice is a private platform whereby just concerned people are allowed to join and see messages from certain channels, which makes it a secured channel of team communication. The sub-channels allow relevant information to be shared with concerned employees which makes it confidential and safe. Employees, as well as employers of an organization, can securely interact.